Legacy software isn’t just outdated – it’s a major risk to your business. These systems, often unsupported by vendors, lack critical security updates, making them prime targets for cyberattacks. They also drain IT budgets, hinder productivity, and fail to meet modern compliance standards. Here’s why they’re a problem and what you can do about it:
- Security Risks: Legacy systems are vulnerable to breaches due to missing updates and outdated encryption. For example, the 2017 Equifax breach exploited an unpatched system, costing over $700 million.
- High Costs: Maintaining old software consumes up to 80% of IT budgets, leaving little room for upgrades. Breaches tied to these systems average $4.45 million in damages.
- Compliance Challenges: Many legacy platforms don’t meet regulations like GDPR or HIPAA, risking fines and reputational damage.
- Operational Issues: Slow performance, frequent downtime, and compatibility problems with modern tools disrupt workflows and increase costs.
What You Can Do:
- Conduct a full risk assessment to identify vulnerabilities.
- Gradually migrate to modern, cloud-based systems with built-in security features.
- Use managed security services to protect systems that can’t be replaced immediately.
Modernizing your IT infrastructure reduces risks, cuts costs, and ensures compliance with current standards. Waiting only increases the stakes.
Legacy System Threats: Modernizing Security for Outdated IT Infrastructure
sbb-itb-05efa2a
Finding Vulnerabilities in Legacy Software
Legacy systems may still hold value, but they come with serious risks that can threaten both operational stability and financial health. These risks generally fall into three main categories: cybersecurity threats, performance issues, and compliance challenges. Understanding these vulnerabilities is essential for crafting a plan to modernize and secure your systems.
Cybersecurity Threats in 2026
Outdated software is a prime target for modern cyberattacks. When software vendors stop supporting a product, they no longer release security patches. This leaves known vulnerabilities wide open for exploitation, often by automated tools. In fact, 85% of IT leaders in government agencies believe that failing to modernize legacy systems puts their organizations at serious risk.
Take the Equifax breach as an example: hackers exploited a known vulnerability (CVE-2017-5638) in an unpatched Apache Struts framework. This allowed them to steal personal data from 147.9 million Americans, ultimately costing the company over $700 million in fines. Similarly, FedEx experienced a data breach when a legacy Amazon S3 server from a prior acquisition was left unsecured, exposing sensitive customer information.
Legacy systems also lack critical modern defenses like Multi-Factor Authentication (MFA) and Zero-Trust security models. Many still rely on outdated encryption methods and weak cryptographic algorithms, making them especially vulnerable to ransomware attacks. Security experts often describe these systems as "low-hanging fruit." As Swindx puts it:
"Legacy software is more than a technical nuisance; it is a strategic cyber-risk that threatens security, compliance and competitiveness".
Performance Problems and Downtime
Beyond security, legacy systems can drag down productivity and create operational bottlenecks. As data volumes grow beyond what these systems were originally designed to handle, performance issues like slow query responses and extended batch processing times become common. Worse, these systems often lack modern failover mechanisms, making them prone to crashes.
The financial toll is enormous. For example, maintaining just 10 aging systems in federal agencies costs around $337 million annually. Ransomware attacks targeting unpatched legacy systems average $1.85 million in recovery costs, and detecting breaches in these systems takes an average of 287 days – significantly longer than the 207 days for modern platforms.
Integration with newer tools is another uphill battle. Legacy platforms often rely on flat networks and static IPs, which demand fragile middleware and manual workarounds that frequently fail. IT teams end up spending more time fixing issues than driving innovation. Meanwhile, finding experts for outdated programming languages like COBOL or VB6 becomes increasingly difficult and expensive.
Compliance Problems in Regulated Industries
Regulatory standards have shifted from simple documentation to rigorous technical enforcement, making legacy systems a liability. Once vendor support ends, these systems often fall out of compliance with frameworks like CMMC and NIST SP 800-171. They also lack the capabilities to meet modern mandates such as MFA, advanced encryption, and detailed logging required by regulations like GDPR, HIPAA, and PCI DSS.
The penalties for non-compliance are steep. By January 2025, GDPR fines had reached €5.88 billion, with Meta alone facing a record €1.2 billion penalty in 2023 for mishandling personal data transfers. Legacy systems are particularly risky in this regard – they contain three times more security vulnerabilities than modern platforms and account for 43% of all data breaches.
Healthcare organizations face additional hurdles. Many legacy systems do not support FHIR APIs, making it impossible to comply with CMS and ONC mandates for patient data access. As NIST highlights:
"Secure, modern software platforms enhance agency resilience, support compliance requirements with cybersecurity mandates and reduce exposure to advanced persistent threats".
Identifying these vulnerabilities is the first step in addressing the risks posed by legacy software. From there, targeted modernization efforts can help mitigate these threats and build a more secure, efficient foundation for the future.
Calculating the True Costs of Legacy Software
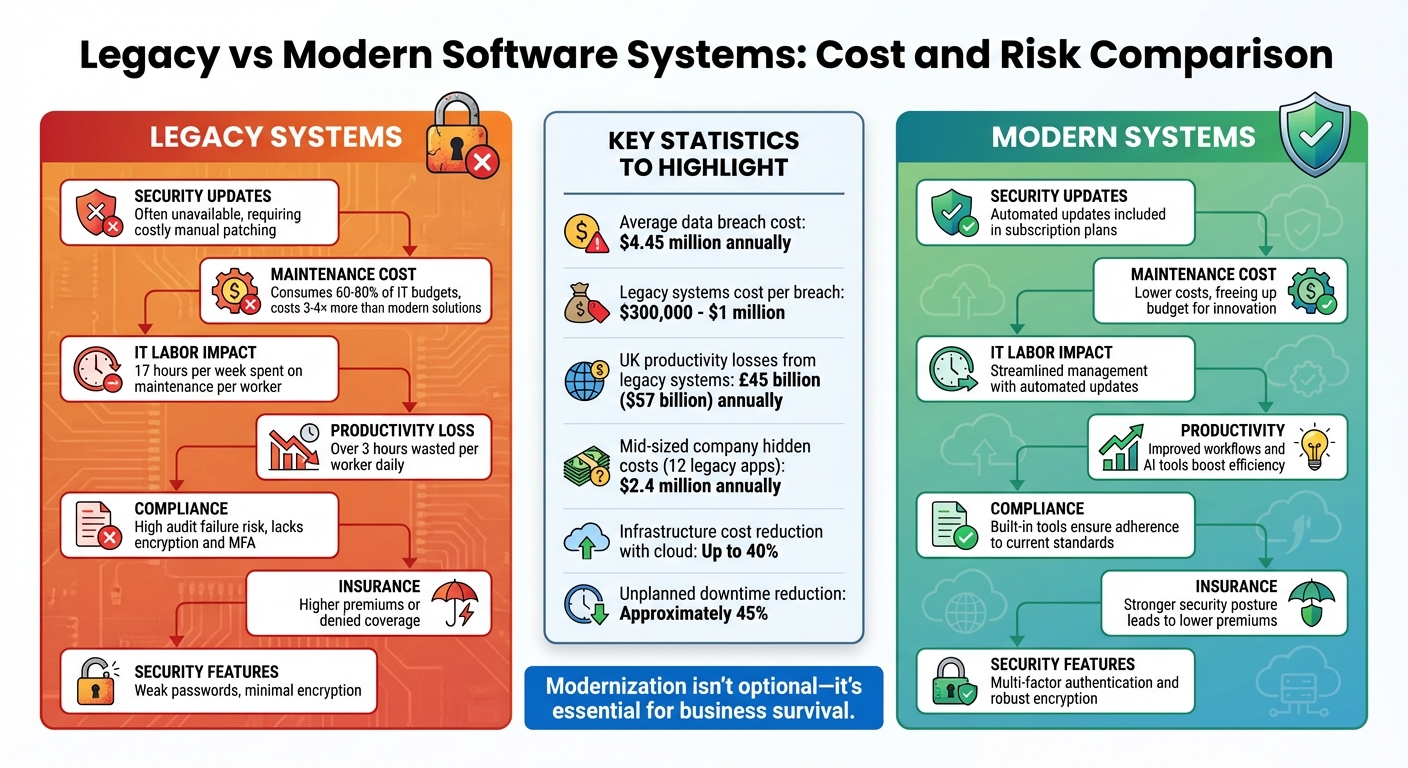
Legacy vs Modern Software Systems: Cost and Risk Comparison
Understanding the financial toll of legacy systems is key to seeing why modernization isn’t just a luxury – it’s a necessity. These outdated systems rack up costs through security breaches, inefficiencies, and the ongoing burden of technical debt.
Financial Damage from Security Breaches
Security breaches tied to legacy systems can be devastating. On average, a data breach costs businesses around $4.45 million annually. For outdated systems, the price tag per breach typically ranges between $300,000 and $1 million, covering everything from investigations and legal fees to fines and recovery efforts.
Take Marriott International, for example. In November 2018, a breach involving an inherited legacy reservation system exposed 500 million guest records. The fallout included a 5% drop in share price and an £18.4 million GDPR fine. Similarly, Marks & Spencer faced a ransomware attack during Easter 2025, forcing them to revert to manual processes. This incident led to an estimated £300 million in lost profits.
Organizations relying on outdated systems also face skyrocketing cyber-insurance premiums – or worse, outright denial of coverage. In 2023 alone, GDPR violations cost companies over $2 billion globally. As Tom Glover, Chief Revenue Officer at Responsive Technology Partners, aptly puts it:
"Technical debt doesn’t behave like a dormant asset sitting quietly on your balance sheet. It behaves like compound interest working against you."
Even maintaining old systems is costly. The Royal Navy, for instance, paid $9 million to keep receiving Windows XP patches after official support ended. And hiring specialists for outdated programming languages like COBOL can cost between $120,000 and $200,000 per employee.
But the financial strain doesn’t stop at security breaches. Legacy systems also bleed money through inefficiencies and maintenance.
Higher Operating Costs and Reduced Productivity
Legacy systems are resource hogs. They consume 60% to 80% of IT budgets just to stay operational, leaving little financial room for innovation. On average, this translates to about $40,000 per IT worker annually just to maintain these outdated systems.
These inefficiencies extend to productivity. Nearly half of employees report losing more than three hours daily due to clunky, outdated software. In the UK alone, legacy systems cost businesses an estimated £45 billion (about $57 billion) in lost productivity every year.
For a mid-sized company running 12 legacy applications, the hidden costs can climb to $2.4 million annually, with $840,000 tied specifically to security and compliance gaps. On the flip side, modernizing these systems can lead to dramatic gains. For example, AESSEAL saw a 77-fold increase in invoicing speed after upgrading, enabling them to support annual sales exceeding £170 million. As William Flaiz, a Digital Transformation Executive, explains:
"Legacy systems aren’t just technical debt. They’re business debt that accumulates interest every quarter you delay action."
The contrast between legacy and modern systems becomes even clearer when you break it down side by side.
Comparison Table: Legacy vs. Modern Systems
| Risk Factor | Legacy Impact | Modern Mitigation |
|---|---|---|
| Security Updates | Often unavailable, requiring costly manual patching or third-party contracts | Automated updates included in subscription plans |
| Maintenance Cost | Consumes up to 80% of IT budgets, costing 3–4× more than modern solutions[7,32] | Lower costs, freeing up budget for innovation |
| IT Labor Impact | Around 17 hours per week spent on maintenance per worker | Streamlined management with automated updates |
| Productivity | Over 3 hours wasted per worker daily on inefficiencies | Improved workflows and AI tools boost efficiency |
| Compliance | High risk of audit failures; lacks encryption and multi-factor authentication[15,31] | Built-in tools ensure adherence to current standards |
| Insurance | Higher premiums or denied coverage for outdated systems | Stronger security posture leads to lower premiums |
| Security Features | Relies on weak passwords and minimal encryption | Includes multi-factor authentication and robust encryption |
Seeing the financial and operational drain of legacy systems makes it clear why addressing these risks is essential. Modern solutions not only reduce costs but also position businesses for long-term growth and resilience.
How to Reduce Legacy Software Risks
Legacy software presents a ticking time bomb for businesses. Tackling these risks means pinpointing weaknesses, moving away from outdated systems, and putting strong defenses in place.
Running a Complete Risk Assessment
Start by mapping out your entire IT environment. This means listing all applications, servers, databases, endpoints, and even those unauthorized "shadow IT" assets. Organize them by age, vendor support status, and whether they’ve hit their end-of-life.
Next, conduct a thorough security audit. This includes penetration testing, scanning for hardcoded credentials, and checking for missing safeguards like encryption or multi-factor authentication (MFA). To prioritize risks, use structured scoring models like the Common Vulnerability Scoring System (CVSS), which helps identify the most pressing vulnerabilities.
Regulatory compliance is another critical area. Ensure your software aligns with current standards such as GDPR, PCI-DSS, and HIPAA through detailed audits. Financially, calculate the Total Cost of Ownership (TCO) by factoring in initial investments, ongoing maintenance, and operational costs. Keeping outdated systems afloat can cost U.S. companies up to $1.225 million annually.
Past data breaches highlight the dangers of neglecting timely updates and assessments. Focus your efforts on high-priority systems that handle sensitive customer data, financial transactions, or regulated records.
Once vulnerabilities are identified, the next step is to migrate to secure, cloud-based platforms to minimize risks.
Moving to Modern Cloud-Based Systems
Shifting to the cloud isn’t just about convenience – it’s a game-changer for security and efficiency. Modern cloud platforms come equipped with features like built-in encryption, automated patching, and MFA, which are often missing in legacy systems. Companies making this move can cut infrastructure costs by up to 40% and reduce unplanned downtime by approximately 45%. On the flip side, legacy systems can drain 60% to 80% of IT budgets just to keep running.
Daniel Ashcraft, Founder of Of Ash and Fire, captures the urgency perfectly:
"Legacy modernization is no longer a ‘nice to have’ conversation… It is a survival conversation."
A gradual migration approach, such as the "Strangler Fig" pattern, minimizes risks by incrementally moving functions to the cloud instead of attempting an all-at-once switch. Techniques like blue-green deployments allow for testing updates in parallel environments, with the option to roll back if issues arise. Focus first on critical yet fragile systems, while keeping an eye on stable ones for future upgrades.
Equifier’s IT consulting services can guide you through this transition. Whether it’s rehosting, replatforming, or refactoring, they provide tailored solutions to eliminate risks tied to outdated software while boosting scalability.
While cloud migration addresses many risks, maintaining strong security measures throughout the process is essential.
Using Equifier‘s Cybersecurity Services

For systems that can’t be modernized right away, managed security services are crucial to fill the gap. Equifier offers solutions like virtual patching through tools such as intrusion prevention systems (IPS) and web application firewalls (WAF) to block exploits targeting vulnerable software.
Network segmentation is another key strategy. By isolating outdated systems, you can limit an attacker’s ability to move laterally within your network. Equifier also employs "legacy wrapping", placing older applications behind modern gateways or APIs to reduce direct exposure.
To stay ahead of threats, Equifier’s Managed Detection & Response (MDR) services provide constant monitoring. Using machine learning, they detect suspicious activities – like privilege escalation or unusual logins – in real time. Adopting Zero Trust principles and enforcing MFA for all logins further mitigates risks tied to weak or hardcoded credentials.
Equifier also ensures compliance with evolving regulations like GDPR, NIS2, HIPAA, and PCI-DSS by implementing automated controls and audit logging. With over 60% of data breaches linked to unpatched or outdated systems, and legacy platforms being three times more likely to face cyberattacks than modern ones, these proactive measures are essential for long-term security and stability.
Conclusion: Protecting Your Organization’s Future
Relying on legacy software is a business risk that grows daily. By 2025, 62% of organizations are expected to still depend on outdated systems, and with the average data breach costing $4.88 million, the real question isn’t whether to modernize – it’s how soon you can begin.
The urgency is clear. Legacy systems drain budgets with high maintenance costs, leaving little room for innovation. At the same time, these systems are more prone to cyberattacks due to outdated security protocols and struggle to integrate with modern technologies. This makes modernization not just a choice, but a necessity.
Nik Froehlich, CEO of Saritasa, captures it perfectly:
"Legacy software is a critical business risk that forward-thinking companies must prioritize. Organizations can no longer afford to delay modernization initiatives".
Equifier steps in to transform outdated systems into secure, modern infrastructure. Through services like risk assessments, secure cloud migrations, and ongoing cybersecurity monitoring, Equifier helps protect your data, cut costs, and prepare your organization for the future. Whether you need immediate security upgrades for systems you can’t replace yet or a full modernization strategy, Equifier provides the expertise to guide your transition safely.
The longer you wait, the higher the stakes. Every quarter of delay increases risks, widens the talent gap, and makes compliance with regulations like GDPR, HIPAA, and NIS2 even harder. Start with a thorough risk assessment and update your critical systems to ensure your IT environment is ready for what’s next.
FAQs
How do I know which legacy apps are the biggest risk?
To spot high-risk legacy apps, start by examining their age and support status. Software that’s been around for more than 5-7 years or hasn’t received updates in a while is often more vulnerable. Look for dependencies on outdated libraries, algorithms, or operating systems, and see if the app struggles to integrate with modern systems, such as cloud platforms.
Pay close attention to apps that are essential for operations or compliance. If these older systems are outdated, they could pose security risks, disrupt workflows, or fail to meet regulatory requirements.
When should we modernize vs. just add security controls?
Modernization makes sense when legacy systems can no longer keep up with today’s security, performance, or integration demands. This often happens due to outdated architecture, inefficiencies in operations, or struggles with meeting compliance standards. While adding security controls might provide a temporary fix – assuming the system is still supported and risks are manageable – this approach is rarely sustainable. When the costs of maintenance, system complexity, or potential risks start to outweigh the benefits, modernization becomes the more practical, long-term path forward.
What’s the safest way to migrate without major downtime?
Migrating legacy software without causing major downtime requires a well-thought-out plan and a step-by-step approach. The key is to identify the most critical components of your system and move them in phases, ensuring operations continue smoothly throughout the process.
Modern tools can make this easier. For example, cloud-based migration and containerization are popular options that offer flexibility and efficiency. But don’t skip the testing phase – thorough testing at every stage is crucial to catch potential issues before they affect users.
A solid migration plan is your safety net. It should include regular backups, compatibility checks to ensure the new system works seamlessly, and rollback options in case something goes wrong. If you’re unsure about handling this on your own, bringing in seasoned specialists can make a world of difference. Their expertise can help you navigate challenges and ensure a secure, disruption-free transition.